From time-to-time we are asked “does our Encoder product protect JavaScript and HTML?”
While our ionCube PHP Encoder product with its unique features such as Dynamic and External Keys do a wonderful job protecting the PHP code on your server, the same server protected code at the client side will still present all of the HTML, CSS and JavaScript when viewing the source in the browser.
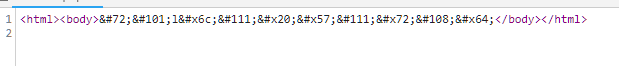
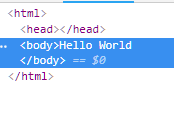
Here is an example of a trivially obfuscated HTML code where browser based tools are used to reverse that obfuscation.
For some this can appear startling, but it is perfectly normal as the web browser must ‘see’ this code for it to render the page and allow the user to interact with it. What is protected on the server is still protected there, but the browser is a completely different problem and this code ‘in the clear’ makes protecting client-side a challenge.
At this point you might just take that as an acceptable risk for your project, though of course, you can still go some way to reduce that risk. There are a number of techniques or design approaches that can be taken to minimise the exposure of what makes your product different from all the others, while both still allowing the user to effectively operate it as well as provide some, but not perfect, protection against the curious.
Keep in mind performance impact for complex obfuscated JavaScript can be significant as well as an increase in size.
The first and easiest design consideration is to move as much of the logic you want to protect to the server side where you can protect it via the ionCube Encoder. Obviously not everything can go there and there will always have to be something client-side.
Considering that the browser must be able to interpret code and styling for the page to render, the main problem to overcome is dealing with the JavaScript that often has extensive capabilities to make the interaction smoother.
There are numerous minimization and JavaScript obfuscation tools out there but even with methods to compress and obfuscate the code in the browser, it still has to be understood and therefore is viewable with the help of debugging tools as shown above.
