Ransomware is a form of malware that holds your data hostage via encryption, blocking access to the operating system. To unlock the computer, the ransomware demands you to make a payment, often via bitcoin, to get the decryption key or to unlock the computer.
You may think you’re protected from ransomware as you have an up to date anti-virus, however in almost all cases this doesn’t stop it from taking over your computer.
Examples such as CryptoLocker, Locky, and police-themed ransomware can find their way onto your computer through phishing emails, including fake bank or postal tracking emails, security vulnerabilities in software, outdated software, malvertising and more.
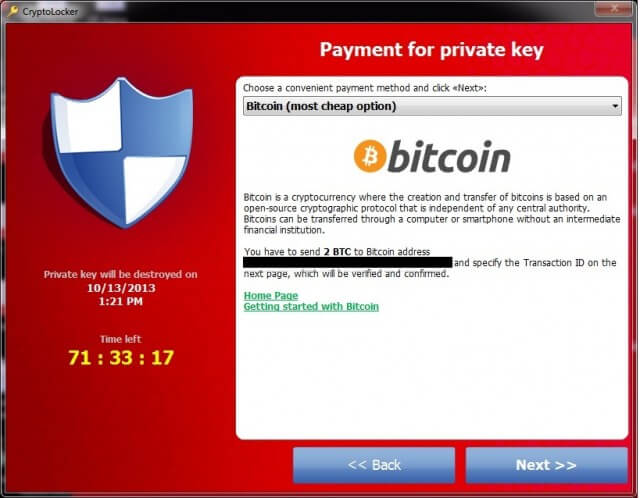
CryptoLocker requests payment in Bitcoins or MoneyPak – Image Source
If you find your PC infected you should never pay the ransom as this only endorses the cyber criminals work. Security researchers have developed tools that can remove ransomware however you may still be left with encrypted or lost files, and tools themselves often require a degree of technical know-how.
Instead, you should plan ahead for a ransomware attack, where you can just wipe your system clean and start again.
| Notable Example: Reveton
Reveton is a major form of ransomware that displays a fake warning from a local police or crime prevention agency and locks you out from your computer, claiming that it’s been used in illegal activities. It offers users to pay the fake fine or face criminal proceedings.
|
Backup, Backup, Backup
Home users are the least likely to have a backup, making them a huge target for ransomware. But this doesn’t mean businesses can get away without a backup either. Businesses can offer the biggest reward due to the potential damage, or the likelihood they pay up. Some ransomware strains are also known to encrypt backups and shared drives first, before attacking the main files.
These are the top things to consider when it comes to backups:
- Don’t store everything on just one computer, keep a copy of those dissertations and photos elsewhere on another computer or USB stick.
- Backup your computer on an external hard drive, in addition to cloud storage such as Google Drive, OneDrive or CrashPlan.
- On top of this, don’t leave your cloud backup active. Close it after everything has synced as the ransomware can also encrypt and corrupt this data.
- Ensure that your external hard drive is kept secure, and consider keeping another copy offsite if you’re running a business from home.
As well as saving you from ransomware, these steps protect you from sudden failure, catastrophic data loss or your PC being destroyed in a fire or flood.
Account Type
Use your everyday account without admin privileges as these accounts open up different areas of the operating system to the ransomware that’s usually inaccessible.
Keep Up To Date
If you’re running outdated software, with known vulnerabilities, you’re the ideal target for ransomware authors. Enable automatic updates for your operating system, and any other software that supports it.
Although it’s common and relatively easy for ransomware to stay hidden from anti-virus and anti-malware suites, you must ensure these are kept up to date to catch the known, old and weak malware.
Be Wary
The most common way ransomware makes it onto your PC is through a phishing attack, usually disguised as an email or through malvertising where advert platforms are compromised.
The next time you get an email from a delivery courier saying they have your parcel, although you’ve not placed any orders, or you need to send your PayPal details over to someone who supposedly works in the support team, consider that these may be cybercriminals wanting to compromise your PC and get to your bank.
What To Do If You’re Hit
In the event that ransomware takes over your PC, you need to take action straight away.
- Disconnect your PC from the network. Ransomware is designed to spread to other computers and shared drives, including backups, so unplug the ethernet cable or disconnect from WiFi.
- Don’t pay the ransom. If you have a backup, now is the time to restore your computer. If you don’t then consider ransomware decryption tools, however, these can be hit and miss if they work at all.
- Some forms of ransomware have a payment timer. It’s known to be effective by setting the BIOS clock back to give yourself more time to find a solution. Only do this is you’re considering trying more tools to fix your problem, not to find the money to pay the criminal.
If you’re in a business, notify anyone who needs to know, such as the IT department, before proceeding with any steps.

